SiFive Blog
The latest insights, and deeper technology dives, from RISC-V leaders

The SiFive blog is your go-to-source for updates on all things RISC-V including processor IP, chip architecture, software and other innovations. Whether you’re producing the next great consumer device, optimizing a datacenter or building next-generation autos check back often to hear the latest from our experts.


The Future of AI is Modular: Why the SiFive-NVIDIA Milestone Matters
X100 - Securing the System - RISC-V AI at the Edge
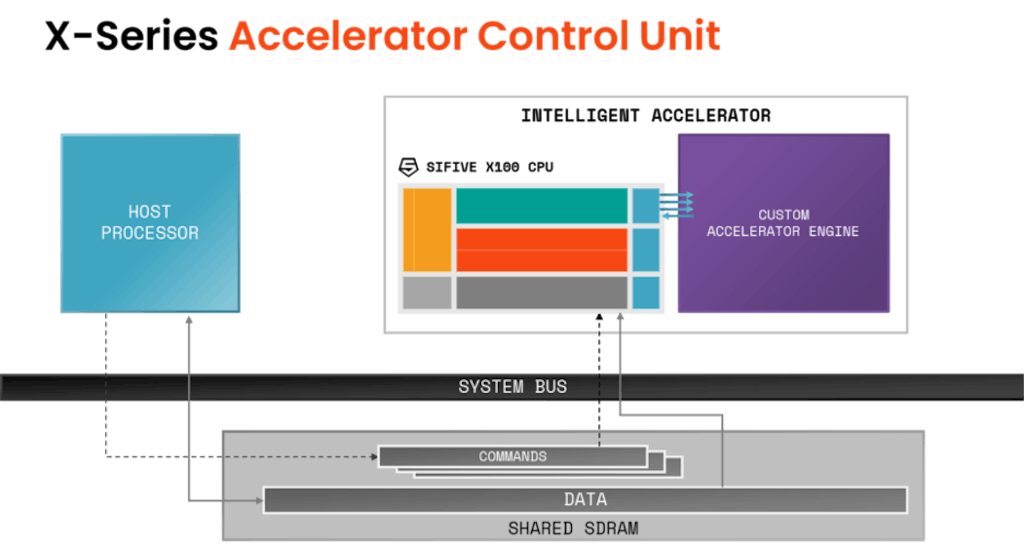
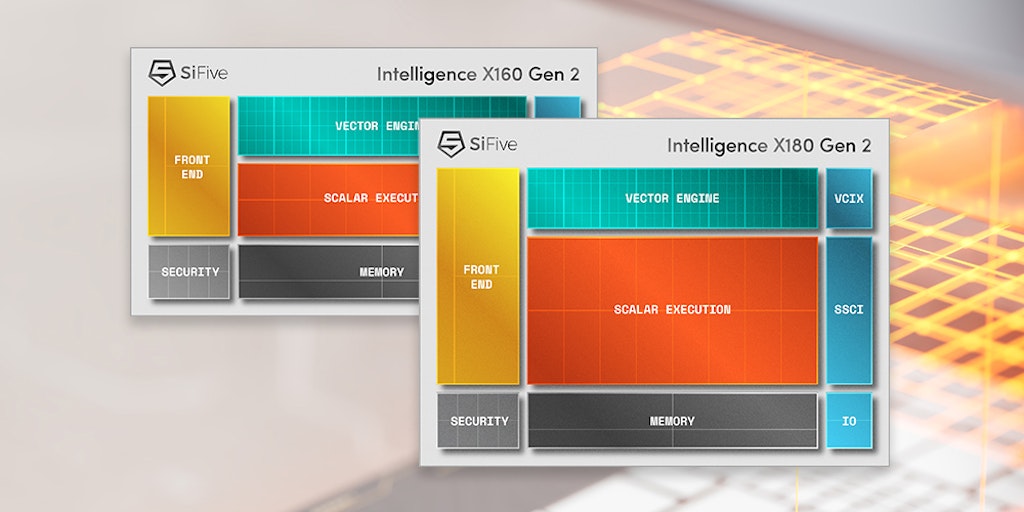
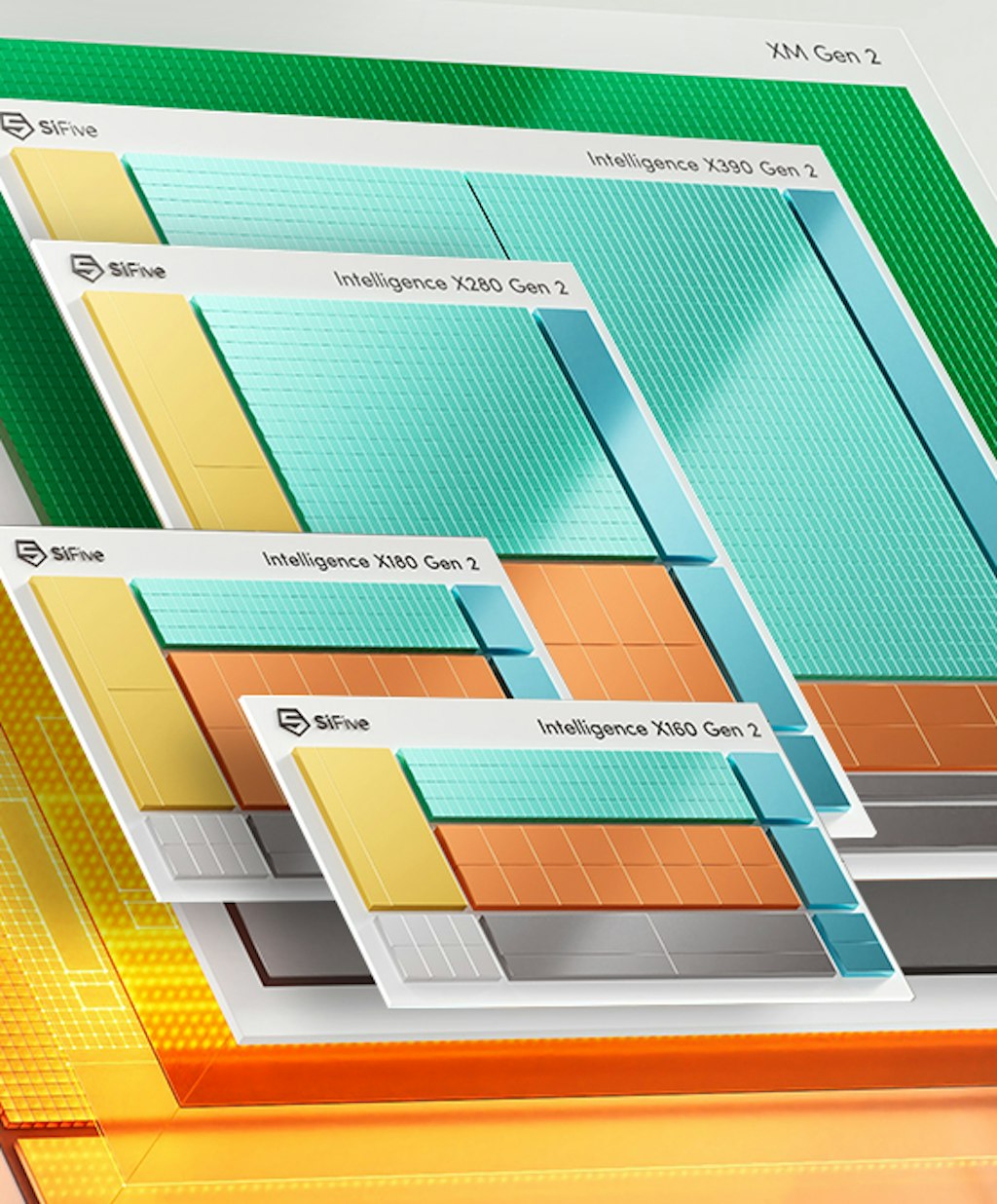
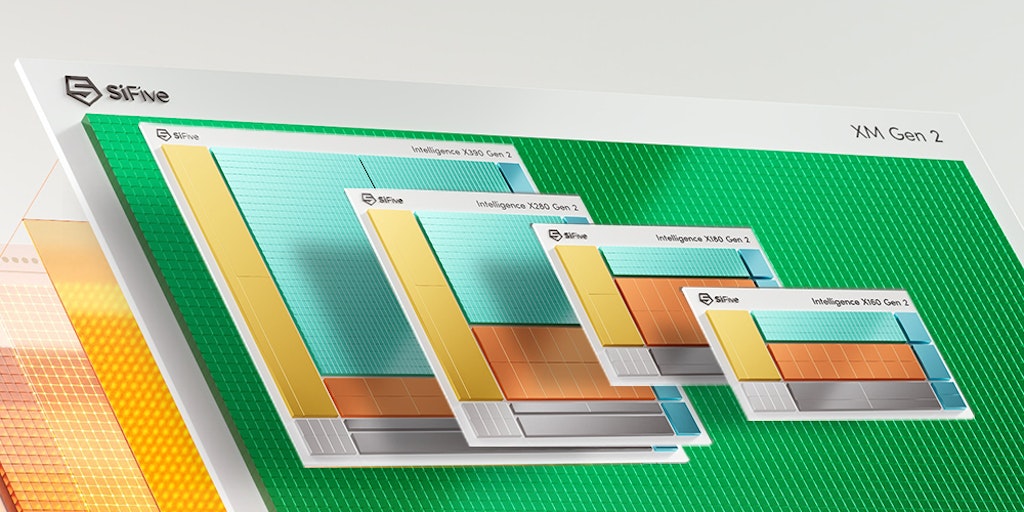
Building the Future of AI on Intelligent Accelerators
Enabling AI Innovation at The Far Edge